Filters
Stock royalty-free photos and images of Pirate informatique
Discover unlimited high resolution images of Pirate informatique and stock visuals for commercial use.

Hacker working on laptop in the dark

Picture of a hacker on a computer

Picture of a hacker on a laptop

Hacker using laptop. Lots of digits on the computer screen.

Hacker using laptop. Hacking the Internet.
Skull made of binary code. Hacker, cyber war symbol

Hacker with computer wearing balaclava

Hooded hacker stealing data from laptop at night.

Picture of a nerd on a computer

Professional hacker with laptop on dark background
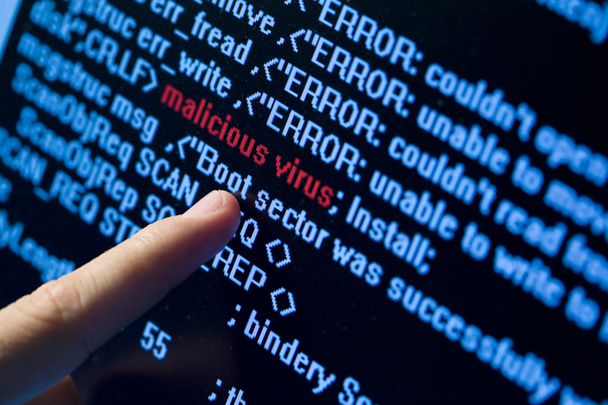
Computer security concept. Virus in program code

System hacked alert after cyber attack on computer network. compromised information concept. internet virus cyber security and cybercrime. hackers to steal the information is a cybercriminal

Hooded hacker sealing data from laptop.

Hacker over a screen with binary code

Man without a face in a hood holds a laptop in his hands on a dark background. Concept of cyber rogue, hacker. Banner. Added glitch effect.

Hands of hacker on a laptop

Digital program code with a earth globe background This is a photoshop edited image.

Hackers are stealing computer data with black background.
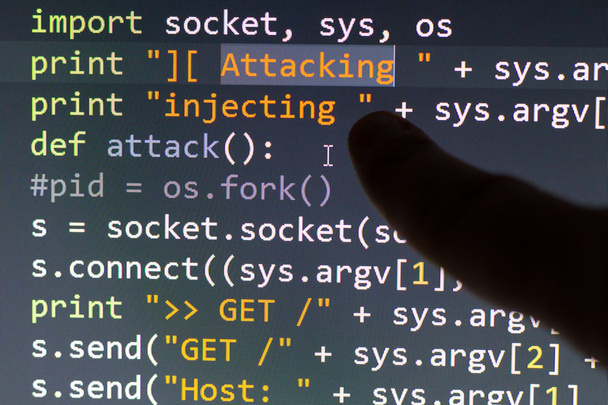
Conceptual cyber attack code

Picture of a stalker

Internet hacker thief concept. Hacker using laptop to attack computer equipment. Dark and scary lighting. A lot of symbols on the computer screen. Selective focus.

Macro computer screen shot with binary code and password text, great concept for computer, technology and online security.

Hacker using laptop with digital business interface in blurry office interior. Hacking and online concept. Double exposure

Internet hacker thief concept. Hacker using laptop to attack computer equipment. Dark and scary lighting. A lot of symbols on the computer screen. Selective focus.

Hacker in hoodie typing code in program using laptop in dark studio

Hacker in the hood sitting at laptop, information hacking. Internet spy, male programmer trying to hack an encrypted network

Silhouette of a hacker isloated on black background

Computer crime concept with police yellow tape

Murder hacker in black mask and hood is penetrating the domestic security information system with motion blur and world map background, concept of defense and espionage of confidential information

Hacker working with laptop in dark room with digital interface around. Internet crime concept. Image with glitch effect.

Hacker bypassing hardware firewall on laptop computer, hooded male cyber criminal

An anonymous hacker with no face typing the code tries to hack the system and steal accesses on the background screens in neon light. The concept of cybersecurity

Hacker hands wearing gloves working on a console commands. Internet cyber concept. Green toning.

Closeup of a mans eye in binary data listening to a cell phone.

Close-up of computer hacker looking at computer monitors and guessing the password using mobile phone in dark room

Business hacker man holding a computer laptop annoyed and frustrated shouting with anger, crazy and yelling with raised hand, anger concept

Dangerous hacker stealing data -concept

The female hacker hacking security firewall late in office

Internet concept. Hacker working on a code on dark digital background with digital interface around.

Freelance programmer working on code for new project

01 or binary code number on the computer in digital data technology concept on black background. Hacker screen display. 3d illustration

Hacker at work view
Download the secret files from the network

Silhouette of a hacker uses a command on graphic user interface
Businessman checking statistics and diagrams on pc
Binary code with LOCKED and magnifying lens on black background

Internet crime concept. Hacker working on a code on dark digital background with digital interface around.

Cybercrime, hacking and technology crime. hacker with laptop. with clipping path.

Young schoolboy prodigy - a hacker. Gifted student enters into the banking system. Hacker at work. Lots of digits on the computer screen. Criminal hacker penetrating network system from his dark hacker room.

Silhouette of a hacker lworking on laptop